Losing the private key is the most common issue webmasters faces during SSL certificate installation. This article will help you to fix that issue helping to understand possible scenarios to recover the key or to regenerate and reissue SSL.
-
-
1
A bit of theory
You receive a private key when generate a Certificate Signing Request (CSR). You submit the CSR code to the CA (certificate authority) and keep private key in a safe place. That means nor us (GoGetSSL), nor CAs have ever your private key. We are not able to recover it, but we can Reissue SSL with a new key. There are multiple ways where you can generate CSR/KEY:
- Using Online CSR Generator;
- Using OpenSSL on your server;
- Using Hosting Management platforms like cPanel, Plesk, Synology NAS DSM, WHM and others.
-
2
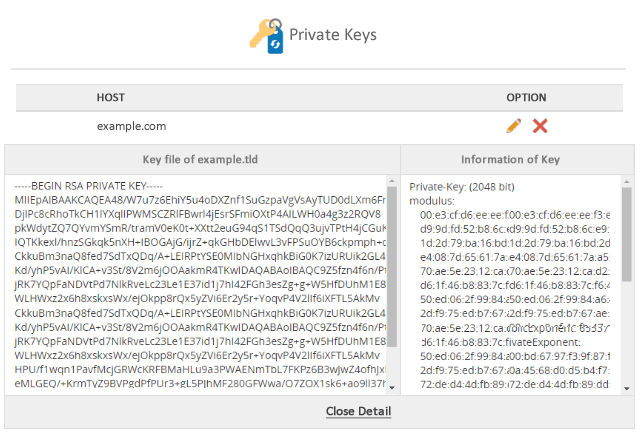
How does the Private Key looks like
The RSA key looks like an array of encoded data, starting and ending with headers, such as -----BEGIN PRIVATE KEY----- and -----END PRIVATE KEY-----
-----BEGIN PRIVATE KEY----- MIIEvwIBADANBgkqhkiG9w0BAQEFAASCBKkwggSlAgEAAoIBAQC98YinMN/FNOkj nIzTY0ok6wOGIHDrWXNUO55bpT1N4u8T4oXLXGo6oUaA/lk4IcCm3gz6RXh3SyBH kdjLIGvivQmPRfcyvJ37tQRrf1eUUymLAHzdbCamHssUabjKCD5L80BGVFSZhmhI 3QCCXVJGy/RCJjpoQWYb3o9KYuukKL91JYM29NCgWZrGDa8rc0OA8RDWq1p8oIkA NcYPgbSPsd4cVGJOAF9ewAiRjBnNp/MgPNb+ksdAX4Lo0OiJ0mGNltr7bWTWPzil i3+lUpg3U9kCgYBOddpWaIv41Pr/w7LHIxiCFi+S6Qi0v0WTu+eUfWoyLjIImwdh aUNrUafZp2/X2sJfEDGYNZ8vuIoIXWhMtifmebzuUW2bgEhwqzvjA2zC1yulFLEI oOQ05iG2ezS0GZrIRLoFI+pvONKM5j3eqveJSy440UJ7gIp95/5JC6GUzQKBgQDQ HlI38RwBwWF07SszN+PqJfQ0LT9obDYwnenAWo0+48C77JJnh1dZ0sPyIFv1IXEj Eoey30sBIDwgMsYFI3HQqczcNDiKByNs1NGfX3pMBOe0fFWQgU5XaqpSo9igDGri CKXEeJbWq8OVyckZ6biZv1d9K5OHlSIk3x6+CzCiwQKBgQCeUokQAJ1FzlOFFMm8 gG5eQ3wZWZopoU87jonz9uZs/yLxL9uzbYFtHlx+5OaFOSRt7pxHZF0ksarDksxB +VIgp54JocoQS7QTMFavE98WQoKp8Zs/WhYDxCwTRwGy+95OxkMt/b1asKBSfa1I SS99fCxLblknTNZ+Ag6Hbc/1FA== -----END PRIVATE KEY-----
-
3
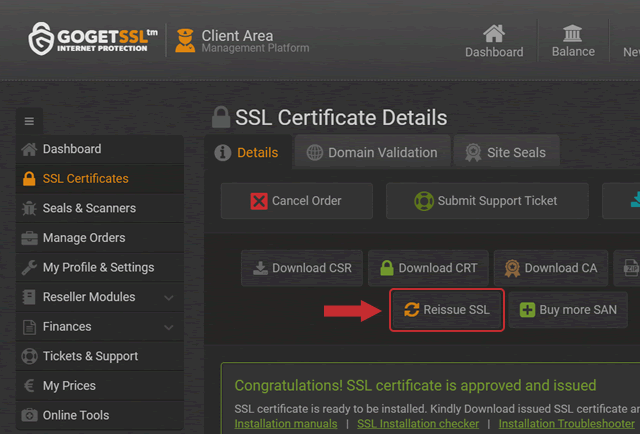
GoGetSSL Management Platform
We do not store any private keys for issued SSL certificates. The only solution we have, in case you have lost the private key, is to reissue SSL certificate following the Wiki guide.
-
4
Windows OS (IIS, Exchange)
There is no option for viewing the private key in plain text on Windows servers. The proper private key is connected automatically when you import certificate via IIS or MMC, however, the CSR and KEY should be generated on the same server.
You can export the key using a password-protected PFX (PKCS#12) file if necessary to get the private key out to install SSL on a different server. Open MMC certificates following the next steps:
Win+R > mmc.exe > OK > File > Add/Remove Snap-in > Certificates > Add > Computer account > Next > Local computer > Finish > OK
Then, go to Personal > Certificates, right-click to the certificate, then "All Tasks" > "Export". You will be able to export your certificate following the instructions from the Export Wizard. Please check more instructions on Windows Docs page.
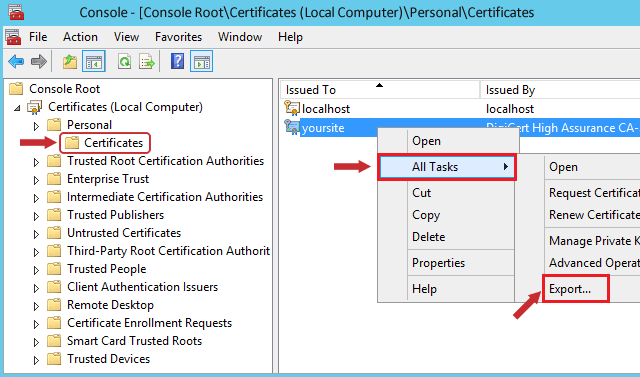
You will receive a .pfx file containing your SSL certificate, private key and CA-bundle, once the export process is done. You can use the online tool to convert your "PKCS12" file to "PEM". Once the conversion is done you will have your private key available.
-
5
Mac OS X
There is no option getting the private key via the graphic user interface of the Keychain tool on Mac OS X. You have to use the Terminal for that. Open /etc/certificates/ directory and search for the file like "*.key.pem". Use the following terminal commands:
cd /etc/certificates/ -THEN- ls -THEN- sudo nano yourdomain.key.pem to open the file
-
6
Tomcat
The private key should be stored in a password-protected Keystore file in case your Tomcat SSL connector configurated in JSSE style. You have to convert the Keystore into PFX file using the command below to get the private key:
keytool -importkeystore -srckeystore keystore.jks -destkeystore keystore.p12 -deststoretype PKCS12 -srcalias <jkskeyalias> -srcstorepass <jkspassword> -srckeypass <keypassword> -deststorepass <newp12password> -destkeypass <newkeypassword>
- Replace "Keystore.jks" with the actual keystore name;
- "Keystore.p12" is the name of the new PKCS12 file you are going to receive;
- <jkskeyalias>, <jkspassword> and <keypassword> are the alias, the key and Keystore passwords that were entered during Keystore generation;
- <jkskeyalias>, <jkspassword> and <keypassword> should be replaced with your JKS file alias, its password, and private key password correspondingly;
- <newp12password> and <newkeypassword> are to be replaced with the passwords you wish to set for your new PKCS12 file and the private key;
You can convert your new PKCS12 file to PEM file to get a separate certificate, CA-bindle and key files using the terminal command below or online tool. You can rename “Private.key” to any name you wish.
openssl pkcs12 -in keystore.p12 -nocerts -nodes -out private.key
-
7
VestaCP
You must save the private key during CSR generation using VestaCP. No key will be available in any Web Client area later. However, there is one option to recover the private key using SSH by checking a temporary file in the "/tmp" folder. The path may look like on example:
/tmp/tmp.gtBnkmSFca/domain.tld.keyPlease note, every time you reboot the server the folder will be deleted. You can try old Linux command to get the exact path to the file:
find /tmp -type f -name "domain.tld.key"
Replace "domain.tld" with the actual domain name.
An alternative option is trying the "grep" command
grep -r -I -l -e ‘-----BEGIN PRIVATE*’ -e ‘-----BEGIN RSA*’ /tmp 2> /dev/null -
8
DirectAdmin
The Private key is saved on the server in the latest version of DirectAdmin. It will be fetched during the installation process to the "Paste a pre-generated certificate and key" field." The section will be empty if you generated CSR and Key elsewhere or panel has an internal problem. You can try using SSH to find the key, as ususlaly it is saved in the next directory:
/usr/local/directadmin/data/users/<user>/domains/<domain>.keywhere <user> and <domain> are your DirectAdmin username and the domain you are trying to recover the key for.
-
9
Webuzo
It is a simple task to recover the Private key on Webuzo management in case a pair of CSR and Private Key were generated using that panel.
- Go to SSL management home page;
- Click the "pen" button on the top right corner;
- You will see the Key code.
-
Conclusion
Lossing the private key is not fatal in case you were using management panels. However, we highly suggest keeping a private key in a very safe place. Reissue SSL if you suspect the key could get to 3rd party hands.
-